On April 12, 2022, the Southern District Court of New York sentenced American programmer and former Ethereum cryptocurrency developer Virgil Griffith to 5 years and 3 months in prison for visiting DPRK and giving a lecture on cryptocurrency technologies. He initially received 20 years in prison, but his sentence was reduced after he pleaded guilty to violating the International Emergency Economic Powers Act (IEEPA), which imposes sanctions on North Korea. In addition, he was fined $100,000.
In accordance with the IEEPA and Executive Order 13466, US citizens cannot provide goods, services, or technology to the DPRK without permission from the Office of Foreign Assets Control (OFAC) under the Department of the Treasury. But in April 2019, in violation of the ban, Griffith visited North Korea (entering through China) to give a presentation at the “Pyongyang Conference on Blockchain and Cryptocurrency.” During the conference, “he and his accomplices presented instructions on how North Korea could use blockchain technology and cryptocurrencies to launder money and circumvent sanctions”. This is what the official accusation looks like. In the unofficial version – he was simply answering questions in detail.
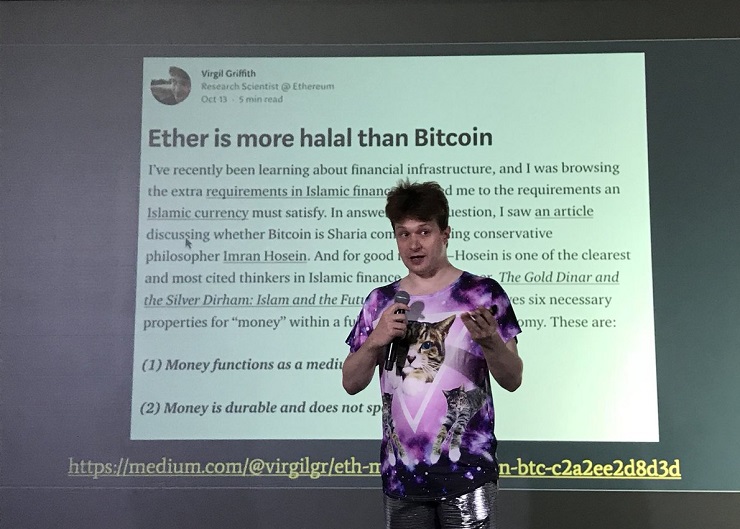
In November 2019, Griffith was arrested in the US. In court photographs were presented, taken during the North Korea conference, which showed Griffith, dressed in what looked like a North Korean military uniform, standing in front of a board that said “No Sanctions.”
In addition, in April 2022, the FBI published a wanted notice for two Europeans who were identified as his accomplices. These are Spanish citizen Alejandro Cao de Benós, head of the KFA, and British citizen Christopher Emms, a cryptocurrency expert. According to court documents, the two planned and organized the aforementioned conference for the benefit of the DPRK, and may also have colluded with Griffith to provide blockchain services and technologies to North Korea. The FBI has labeled both of them “dangerous international fugitives” and they face up to 20 years in prison for violating the IEEPA.
This story had interesting implications regarding the search for Griffith’s alleged accomplices in the ROK. On June 29, 2022, Minister of Justice Han Dong-hoon traveled to the United States for a nine-day visit that included meeting with the director of the Federal Bureau of Investigation and two vice presidents of the World Bank to discuss cooperation in the fight against cybercrime.
After this, some opposition figures said that Han visited the US Attorney’s Office for the Southern District of New York to learn more about the results of the Griffith investigation.
Allegedly, the New York district attorney’s office submitted evidence to a New York court in the form of email correspondence between Griffith and an unnamed person based in South Korea, and these emails contained the assertion that the mayors of Seoul and Seongnam were interested in creating a cryptocurrency infrastructure in their respective cities. The mayor of Seoul referred to in the email was the late Park Won-soon, while the mayor of Seongnam Lee Jae-myung is the current leader of the opposition Democratic Party of Korea.
So Han went to New York to see if there were other documents that could show the possible links these politicians had to North Korea’s attempt to build a cryptocurrency infrastructure to avoid international sanctions.
The Minister of Justice neither confirmed nor denied this claim.
Later on, Democratic MP Kim Ui-gyeom gave some details. Griffith’s counterpart was a woman named Erica Kang, and the correspondence amounted to about 50-60 pages of documents. For example, Griffith’s business partner wrote to him on June 29, 2019 as follows: “The Seoul government is open to providing support for the Ethereum Foundation, but we are in the process of discussing how to provide such support. During the conversation, we talked about supporting the Ethereum research center and establishing an institution in the DPRK. So it’s not a 100% confirmed proposal, but we’re trying to make it happen.”
Following this, the Mayor of Seoul Oh Se-hoon said he would carefully look into the allegation that his predecessor tried to circumvent sanctions. However, he did not immediately blame his opponents and noted that he would turn to law enforcement agencies with a request to investigate this case if any violations were found. So far, the mayor has indicated something along the lines of “I have no information on the extent to which the city government was involved in the cryptocurrency project during the former mayor’s tenure” and “I was told that there were no working-level employees in the city government who would contact North Korea about cryptocurrencies.”
This is not the only US operation against the “accomplices of the Pyongyang hackers.” On November 7, 2022, a prominent Nigerian social media figure who was involved in money laundering for North Korea was sentenced to 11 years in prison by a US court. Nigerian citizen Ramon Olorunwa Abbas, acting alongside Canadian citizen Ghaleb Alaumary, was instrumental in legalizing the money that was stolen by North Korean hackers from a bank in Malta in 2019. Abbas gained notoriety in Nigeria for his habit of posting photos of himself wearing expensive clothes in luxury hotels and private jets on social media. In June 2020, at the request of US authorities, Abbas was detained in Dubai, after which he was extradited to the United States. His accomplice received a similar sentence in 2021.
But even more interesting is the story of hacker Denis Dubnikov, who, according to The Wall Street Journal, was arrested at the request of the United States in the Netherlands on November 2, 2021, and faces up to 20 years in prison and a $500,000 fine.
According to the US Department of Justice, the Russian was engaged in money laundering in the interests of the Ryuk hacker group, and also received a reward of $400,000 in the form of Bitcoin from the funds that the victims transferred to the extortionists. In 2020, Ryuk accounted for a third of all ransomware attacks in the United States, according to cybersecurity firm SonicWall.
And now the most important part! Initially, it was assumed that the Ryuk group was associated with North Korea, but experts from CrowdStrike and McAfee Labs reported that the malware was allegedly developed by “Russian-speaking hackers.” And this again makes the author wonder if the “DPRK-related” hacker groups with specific names like “KimSuky” or “LazaRus” should not be taken as a joke of Russian-speaking hackers using the image of North Korea as a cover.
On March 22, US National Security Advisor Jake Sullivan said that North Korea had significant cyber capabilities and was working with all kinds of cybercriminals, including those from Russia. But the cart has already been put before the horse.
It should be noted that North Korea is independently forming its cybertroops and boosting digital literacy in general (yes, we remember the effect of a self-fulfilling prophecy). On December 27, 2021, Rodong Sinmun reported that “about 100,000 workers are currently enrolled in online classes across the country, including 10,000 registered this year alone.” North Korea has highlighted the development of distance education system as a tool to help workers acquire the “modern science and technology” needed in their workplaces.
On November 23, 2021, North Korea launched a nationwide computer programming competition aimed at developing talent capable of leading the country’s information technology development: about 1,240 participants, ranging from teachers and researchers to college and high school students, participated in three rounds of preliminary competitions in the run-up to the final.
It is no wonder that the West and the ROK have already started talking about the fact that “Juche IT specialists” who have undergone such training can be hired for remote work, but the author will talk about how the US and the ROK oppose the “Pyongyang hackers” in the next article.
Konstantin Asmolov, PhD in History, leading research fellow at the Center for Korean Studies of the Institute of China and Modern Asia, the Russian Academy of Sciences, exclusively for the online magazine “New Eastern Outlook.”